A user's vision of a libre, decentralised Internet
In order to make the Internet a freer, more decentralised, less oligarchical place, users should have full control on their online identity and this should be separate from other online services like email, instant messaging, microblogging, social networking etc. Online services, in turn, should be based on open standards, yes like good old email and the web, so that different implementations are interoperable with each other. A user should be able to switch from one service provider to another with one click while retaining all of her data (messages, contacts, photos etc.) in a way that is totally transparent to her contacts and correspondents. Think of telephone number portability, in a way. Rebuilding the Internet around user identities as the core service will allow for more competition between service providers, less lock-in effects and walled-gardens, better privacy protection. Here is how to do it.
§ § §
The Internet as it is, or as it has become in the last dozen of years, is in a sorry state when you gauge it from the vantage point of liberty.
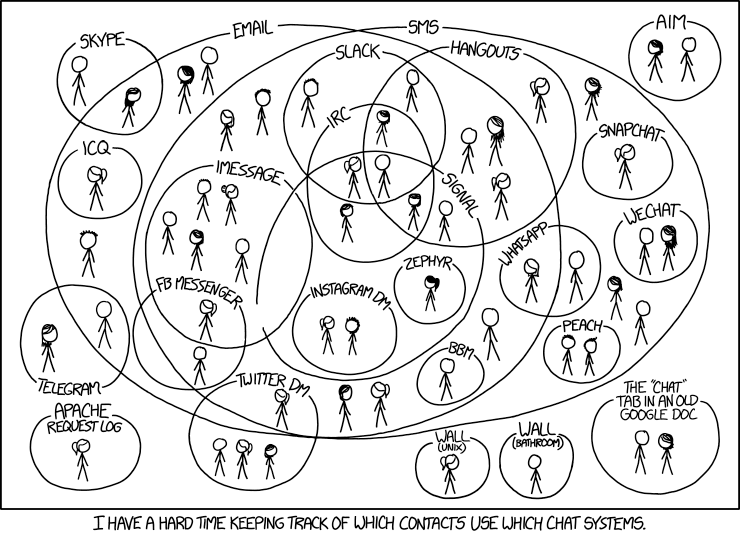
The proliferation of walled gardens based on closed, proprietary standards not only contradict the Internet’s original constitution, but ultimately restrict communication among users, or force them to subscribe to countless services in order to talk to other users who dwell in different gardens, as memorably sketched by XKCD
Network centrality, or high degree of connectedness, brings enormous profits and power to those occupying those positions. Network externalities benefit also the less connected members of the network. Compounded with closed standards and so-called walled gardens, they create a strong lock-in effect that ultimately hinders competition, innovation and effective freedom of choice.
The most obvious example of the ills of closed standards and walled gardens is to compare it with the existing e-mail service. Despite all the obituaries and vented frustrations for this venerable form of digital communication, we may tend to forget that once we have subscribed with one email service provider we can exchange messages with everybody else, irrespective of their service provider. So the user at yahoo dot com can write to other users at gmail dot com or at mail dot com or any other service that complies with the open email technological standard, even if implemented in different ways. This is clearly not the case today with video conferencing or other instant messaging services. A Skype user can communicate only with other Skype users and needs a Wire account if he or she wants to talk with a subscriber to that service. Now just imagine how impractical it would be to have a separate email account with each and every service provider in order to communicate with subscribers of those services.
Network centrality has turned into another sort of positional rent, bringing enormous profits to those players who have muscled their way at the centre of the global connectivity graph. Central operators now wield enormous power, not only financially, but in shaping the opinions of literally billions of people. The spread of fake news during the last US electoral campaign being only the most visible and prominent case of the noxious role played by Facebook and the like in adulterating American democracy. The problem is that once strong network externalities are in place, despite the highly inefficient and ultimately unfair outcomes of this state of affairs, it becomes very difficult to unseat the central players or to change the network topology itself.
Enlightened emperors and kings (see Versailles below) lay exquisite gardens, but expect loyalty from their subjects.
Besides, the last decade inscribed on the historical record of humanity the sad spectacle of billions of people who freely —although often unwittingly— gave their personal data away to giant digital corporations. Or should we say that these data were taken away from them surreptitiously, behind an opaque EULA curtain? In any case, under the delusional spell of thinking they were just communicating with their “friends”, millions of users allowed private corporations to amass their private photographs, political preferences, religious beliefs, social connections, spontaneously realising the wildest dreams of STASI, KGB and the like for total surveillance and control. Add to this the colossal scale of personal data and metadata recording carried out by the National Security Agency (NSA) of the United States of America on a global level and clearly the Internet does have a privacy problem, to say the least.
If a network topology becomes too centralised, with the unbalanced distribution of the network benefits and rewards that this implies, what are the possible strategies that those who hold strong political opinions in favour of highly decentralised networks should pursue?
A first, let’s call it liberal response would see a mix of regulatory and institutional adjustments in order to increase overall competition, ending with a sort of Internet oligarchy where there are a few central nodes — instead of just one — and these are marginally easier to contest.
In a second kind of response, let’s call it exodus, programmers and users who deeply care about liberty would develop the technical tools and grassroots organisation for a free Internet, adopt them and offer them for free to everybody else, liberate a territory in the Internet space in order to build a minimum of network externality plus-value in order to make it viable, holding it and inviting more people in, while implicitly assuming that the very smallness of their freedom island would attract little attention from corporate Internet’s dreadnoughts who would treat it at most as a nuisance. The obvious limit of this strategy is that it ultimately fails to attract a sufficient number of users so as to alter the overall balance of network power, and this is also due to the fact that for the tech-unsavvy user it is difficult to get a toehold on the free island because the applications are not perceived as user-friendly or just because the sheer number of alternatives is confusing.
A third, radical strategy is the topic of this modest proposal. It is a minimally maximalistic strategy meaning that rather than completely overhauling the Internet as it has become, it seeks to identify the minimum set of admittedly radical changes that would bring about the maximum goal of restoring Internet not only as a place of freedom, but also a liberating set of institutions and technologies. Given the scope of the task, it goes without saying that I will cover here only a very small part of it, starting from a vision of what a libre Internet might look like from the point of view of the user. At the more technical levels there are very interesting discussions and projects going on, starting from Tim Berners-Lee’s Solid project for decentralisation.
In order to address the shortcomings of the current status of online life, I propose to move towards a total separation and hierarchical ordering of different levels. In particular, the different levels that have to be separated and made independent of each other are:
- Identity: the user’s online identity, including a domain name and public and private keys. A main identity could be linked to the real one and legally certified by a state-like authority, but not necessarily. Multiple identities would — and perhaps should — be possible for anonymisation and privacy concerns.
- Services: the main Internet services including email, web, microblogging, instant messaging, videoconferencing etc., all defined by open standards.
- Implementation: the technical implementation of a particular service as provided by a service-provider or self-hosted and self-managed based on existing software libraries complying with the open standard.
- Infrastructure: the underlying Internet infrastructure, neutral towards services, implementations and content.
Correspondingly, there will be various tiers of service providers:
INSP: Internet Name Service Provider
IUSP: Internet User Service Provider
ISIMP: Internet Service Implementaiton Provider
IIP: Internet Infrastructure Provider, including what we are used to call ISP or internet access providers
It is important to stress that the identity layer, and the corresponding service provision, has to come first and be independent of others. Only if the user has full control over her online identity, and this is not linked to services, we could start thinking of a libre, decentralised Internet. As an admittedly partial analogy, just think about telephone number portability: when you switch provider, you can keep your number (if you want to) and nothing will change from your contacts’ point of view. If number portability had not been made mandatory by law it would have been impossible to have a competitive market for telephone services, fixed and mobile.
Sketching a vision of user control
Allowing for a moment to play with the very broad brushes so far described, we can imagine how a possible end result would be from the point of view of the user. The user of the libre Internet of tomorrow will be able to manage his online life through a dashboard. The user will have at least one unique identifier associated with him/her, linked to a domain name and his public and private keys.
The dashboard will list all the possible Internet services that the user may want to activate and connect to her identity. Let’s say that the user wants to activate email and microblogging. After clicking on the email box, a list of service providers will appear, each with a short description of the features offered, price (including free services, of course) and conditions of service, including the self-hosted, self-managed solution. The user evaluates the offers and chooses a service provider, accepting the related contract (EULA, Terms of use etc.) thus activating the service.
For example, let’s assume that user John Doe “owns”, controls and is unambiguously associated with the Unique Network Identifier (UNI) @johndoe.id. I assume here that all primary identities are registered under the arbitrary domain .id although this is not strictly necessary, it could be .p for “personal” or any other domain. Within this personal domain, the user can optionally activate various mailboxes or aliases. If no mailbox or alias is specified before the @ or even if the primary domain is left blank messages are delivered to the default mailbox associated with the UNI @johndoe : [default mailbox]@johndoe[.id]
There might a problem of scalability and DNS responsiveness as the .id domain would have potentially billions of second level domains, one for each user. While I prefer not to deal with implementation problems at this stage, it will suffice to note that the technology for distributed, scalable, synchronized databases already exists (e.g. Google’s Spanner, that has been released as open source).
Following up on our example, when John Doe activates the email service he chooses the provider Giantmail because it’s free and he has read a lot of good press coverage about it. In any case, his online identity and email address do not change with the service provider. Other users, irrespective of their email provider, will be able to reach him using his unique network identifier. Protocols and name resolution infrastructure will take care of determining to which actual mailbox messages will be delivered. In any case, John Doe’s emails will be stored encrypted (with John Doe’s own keys) on Giantmail servers. If at some point John Doe is not satisfied anymore with Giantmail services, he will be able to switch effortlessly to another provider using the dashboard. With the click selecting his new provider, his personal data (messages, attachments, contacts etc.) are transfered to the new provider’s servers in the same encrypted format as they were in the previous one.
From the point of view of his correspondents, the switch to a new service provider will be totally transparent: they will continue to email @johndoe as before.
The same goes for the social networking service. From the very early days of digital social networks, John Doe has enthusiastically embraced the possibility of keeping in touch and sharing updates and photos with friends and has a rich profile on his service provider of choice, PygouFace. At some point John hears that a competing service —VisageLibre— offers features that are more attractive to him, for example, a business model where the provider’s costs are made explicit and covered with a transparent subscription where John can choose to either pay cash, or contribute a certain amount of spare computing time on his devices, or accept advertisements. John logs into his dashboard and with a click terminates the subscription with the previous social networking service provider — accepting eventual early termination costs if they were foreseen in the previous contract — and switches to the new provider. His posts, photos and other data — that are in any case encrypted with Jonh’s personal keys — will be seamlessly migrated to the data centres of the new service provider (or they might possibly remain where they were if service provider and infrastructure providers are separate entities, more on this below). As with the email service, the change will be totally transparent for John’s correspondents and online friends who will continue to see the same content, albeit possibly with a different graphical style if John opted for an update while switching provider, and will continue to address John online with his UNI.

Balancing incentives for innovation and competition
If this scheme devolves personal data ownership and control to users, and introduces a healthy competitive environment where provider lock-in effects and network centrality positional rents are highly reduced, a potential critique could be that there aren’t sufficient incentives for service providers to innovate in a such a cutthroat competitive environment with wafer-thin margins (and where service providers cannot monetise users’ personal data that are encrypted at rest). The new institutional arrangement sketched here might indeed have an innovation problem. How can service providers attract customers with new features if the service standards are open and defined through industry consensus and regulatory bodies?
These are legitimate concerns that should be addressed.
First of all, there is ample scope for innovation in how the open standards themselves are implemented. The history of email and the world wide web show how there is a healthy competition between closed and open source software models and between different implementations of the same standard.
Then one could imagine a separation between a set of core features defined by the open standard and “add-on” features offered by individual providers. The user would base his choice of service provider also on these additional features, alongside other criteria of interface quality and style, costs (hidden or explicit), brand etc. Since the add-on features are not covered by the open standard, the user would be warned that in case of switching to another provider the add-on features might not be available because they are not part of the open standard and thus not guaranteed to be migrated seamlessly. The associated data would still be backed up and delivered to the users for their records.
If an innovative “add-on” feature becomes popular, competitive providers might want to replicate it offering it to their own customers. In case of widespread adoption, it is in the interest of users and competition that the new features are introduced into the open standard and made interoperable. In this case, it is reasonable that the innovative service provider enjoys a sort of embargo period — reminiscent of intellectual property laws— to protect its innovation before it becomes part of the open standard. In this case, the length of the protection period should be a trade-off between the opposite demands of open competition and innovation.
The success of this system of incentives will depend on many factors, not least the relative balance of market dominance that the scheme is supposed to alter. In recent years we have seen how open source project may be taken to partially unfree directions precisely by this kind of mix of open and proprietary components (e.g. Android).
Infrastructure
In principle, there is a separation between service and infrastructure providers (mainly data centres, assuming that connectivity, retail Internet access, backbones and the like would continue to follow the current model). The usual factors of economies of scale, transaction costs, tighter of looser association between the service layer and the technological platform underpinning it will inform and shape the individual companies choices about whether to integrate services and infrastructure or to focus only on one of them. Considering that user data at rest are strongly encrypted and cannot be monetised by service providers as such, there are perhaps strong incentives for a decoupling between service providers and infrastructure providers. Competition in a market for infrastructure providers, mainly data centres, where economies of scale have a big impact will probably see the consolidation of a few very large players. At the same time, the complexity of factors affecting the location and operation of data centres, including the interplay with the politically charged energy market, should create a sufficiently competitive environment and stave off pushes towards complete monopolisation.
Besides, with an innovation model based on new features added on top of a core open standard that progressively expands incorporating part of the same new features it is likely that many service providers will prefer to keep the infrastructure component in-house in order to offer a better integrated innovative user experience and protect it from outsiders at the same time. Other service companies may prefer to focus only on commercial or content innovation and rely on wholesale infrastructure providers.
Acknowledgements
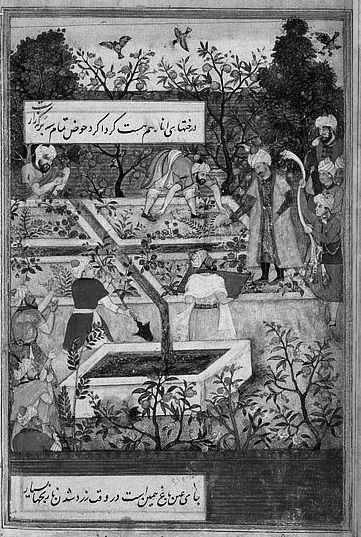
Cover image: Emperor Babur (1483–1530) superintending the laying-out of the Garden of Fidelity (Bagh-e Wafa), near Jalalabad or possibly in Kabul. Illustration from the “Memoirs of Babur” (Baburnmma). Miniature painting by Bishndas and Nanha, ca. 1590. From the Victoria and Albert Museum, London.
Inline: Extrait du “Plan de Versailles, du petit parc, et de ses dependances où sont marqués les emplacemens de chaque maison de cette ville, les plans du Château, et des hôtels, et les distributions des jardins et bosquets” par Mr l’abbé Delagrive (1689-1757) – M D CC XLVI (1746) Wikimedia.